Edoxi’s 40-hour CompTIA CySA+ training in Dubai builds advanced skills in cybersecurity threat detection, analysis, and response. As a CompTIA Authorized Partner, our courses are available in both online and offline formats. The training covers security operations, vulnerability management, incident response, and reporting. Gain hands-on skills with industry-standard tools like Splunk, ELK Stack, and Wireshark. Enrol now and gain skills that qualify you for mid-level SOC analyst roles in Dubai.
Edoxi’s 40-hour CompTIA CySA+ Certification Training in Dubai equips IT professionals with advanced skills in cybersecurity threat detection, analysis, and response. The course is specifically designed for security analysts and aspiring SOC professionals. It helps you master the ability to identify, investigate, and mitigate complex security incidents across different IT environments.
The CompTIA CySA+ curriculum covers all four CompTIA CySA+ domains. It prepares students for the CS0-003 certification exam through targeted training and hands-on practice. Through immersive, hands-on training, learners work on real-world cybersecurity scenarios using industry-leading tools such as Splunk, ELK Stack, and Wireshark. Participants gain practical experience in vulnerability management, malware traffic analysis, log monitoring, and threat hunting. These skills mirror the daily operations of a Security Operations Centre (SOC).
Edoxi offers classroom and online CompTIA CySA+ training in Dubai to fit individual and corporate needs. For organizations, we provide customized 5-day corporate training programs featuring team-based security simulations, enterprise-specific case studies, and flexible delivery options, including our popular Fly-Me-a-Trainer service.
Our hands-on approach guarantees that you graduate with practical expertise, enabling you to apply threat intelligence and security analytics in real-world professional environments. The CompTIA CySA+ course also prepares you for mid-level cybersecurity roles, making you a strong candidate for positions in finance, healthcare, government, and other high-demand industries across the UAE and globally.
CompTIA CySA+ Exam Details:
The CompTIA Cybersecurity Analyst (CySA+) certification is designed for IT professionals focused on threat detection, analysis, and response using behavioral analytics and security tools. Here’s a detailed breakdown of the CySA+ exam.
| Exam Criteria | Details |
| Exam Code | CS0-003 |
| Exam Name | CompTIA Cybersecurity Analyst (CySA+) Certification Exam |
| Duration | 165 minutes |
| Number of Questions | 85, Multiple Choice |
| Passing Score | 750/1000 |
| Certification Validity | 3 years |
| Exam Administration Authority | Pearson VUE |
Master industry-standard tools, including Splunk, ELK Stack, Wireshark, and vulnerability scanners through guided practical exercises.
Analyze authentic security incidents and vulnerabilities mirroring actual enterprise environments and attack vectors.
Access authorized CompTIA study guides, lab manuals, and specialized resources for exam preparation and reference.
Receive targeted coaching for the CS0-003 exam with practice questions, domain-specific reviews, and proven test-taking strategies.
Conduct vulnerability scans, prioritize findings using CVSS, and develop remediation strategies in simulated enterprise networks.
Create and implement customized incident response playbooks following industry best practices and frameworks.
Working in cybersecurity roles seeking to advance their threat analysis capabilities.
Managing network infrastructure with basic security knowledge, ready for specialized training.
Responsible for system security, wanting to develop advanced threat detection skills.
Professionals looking to enhance their technical capabilities and advance to mid-level SOC positions.
Professionals providing security services that need formal certification and analytical methodology training.
Individuals with Networking knowledge transitioning to specialized cybersecurity analysis roles.
This CySA+ course features extensive hands-on labs with professional security tools, including Splunk, ELK Stack, Wireshark, and various vulnerability scanners. Classroom activities include threat hunting drills, vulnerability prioritization exercises, and root cause analysis simulations mirroring real-world security operations center environments.
Analyze security logs from multiple sources to identify suspicious behaviors, establish patterns, and generate comprehensive incident reports with mitigation recommendations.
Conduct vulnerability assessments in a simulated enterprise environment, prioritize findings using CVSS, and develop complete remediation plans with proper documentation.
Perform active and passive threat hunting using advanced tools to detect indicators of compromise and document findings according to industry standards.
Use Wireshark, REMnux, and PacketTotal to capture, analyze, and document malicious network traffic patterns, extracting key indicators for threat intelligence.
Implement monitoring solutions to identify suspicious DNS queries and web requests, distinguishing between normal activity and potential command-and-control communications.
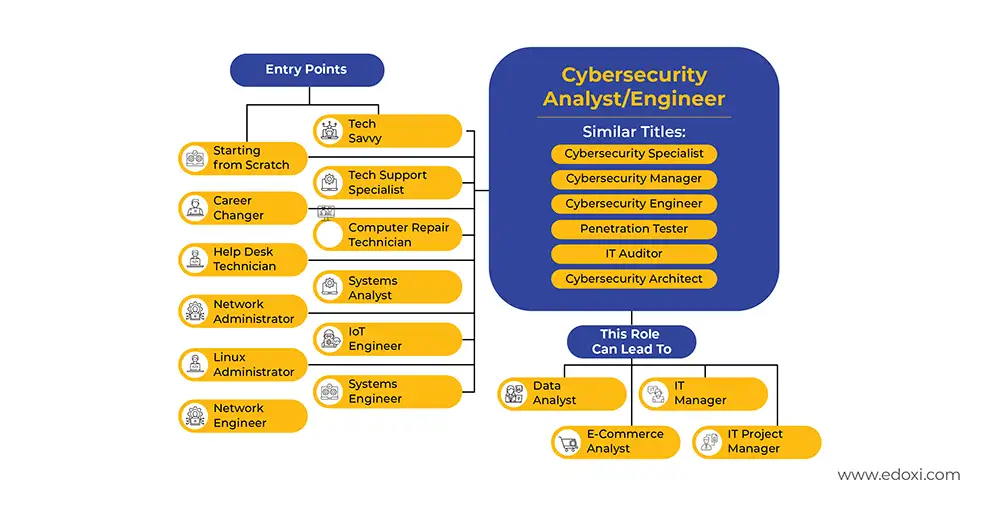
Earning the CompTIA CySA+ certification creates a clear path toward roles in cybersecurity threat detection and analysis. These positions offer strong career growth and open doors to specialised security roles across various industries in the UAE. The following are a few outcomes that you can expect after completing Edoxi’s CompTIA CySA+ Course in Dubai

Get expert assistance in getting you CompTIA CySA+ Course customised!
Here’s a four-step guide to becoming a certified CompTIA CySA+ professional.
Join Edoxi’s CompTIA CySA+ Course
Edoxi is a premier training institution offering quality cybersecurity courses in Dubai. The following are a few reasons that make Edoxi’s CySA+ Training unique;
Our official CompTIA partnership ensures curriculum alignment with CySA+ certification requirements and access to authorized study materials.
Our instructors bring practical SOC, vulnerability management, and incident response experience directly to the classroom environment.
Students train in specialized facilities equipped with enterprise-grade security tools that mirror professional working environments.
Multiple course timing options accommodate working professionals without compromising their current career responsibilities.
We deliver customised corporate training to government bodies, banks, and enterprises in the UAE and the Middle East.
Edoxi delivers Cybersecurity training across GCC nations, including the UAE, Saudi Arabia, Qatar, Oman, and is expanding successfully into European markets.

Our mentors are leaders and experts in their fields. They can challenge and guide you on your road to success!

Maria Mehwish
Maria Mehwish is a forward-thinking and knowledgeable information security leader with a strong background in building, updating, and maintaining digital protections for various organisations. As a certified CEH, CCSP, CCT, and CISSP Trainer, Maria has a proven track record of delivering innovative and immersive coursework, enhancing learning experiences for cyber threats, ethical hacking, security policy, DevSecOps, and cloud security. With excellent verbal and written communication skills, she is also adept at troubleshooting problems and building successful solutions.
Maria is a self-motivated individual with a strong sense of personal responsibility, capable of managing projects from start to finish. Her expertise in Amazon Web Services, Java/Go/Python/C++, DevSecOps, computer security, Linux, penetration testing, and risk analysis, among others, makes her a valuable asset to any organisation. Maria, a British national, is a native English speaker and has intermediate proficiency in Urdu.
No formal cybersecurity experience is required to join the CompTIA CySA+ course, making it suitable for IT professionals looking to transition into security roles. However, the following knowledge will be beneficial:
Basic Networking Knowledge: Understanding of networking protocols, IP addressing, and common network devices
IT Systems Familiarity: Awareness of operating systems, hardware components, and standard IT workflows