Edoxi’s 40-hour CompTIA Security+ training in Kuwait builds core cybersecurity skills in network defence, cryptography, identity management, risk mitigation, and compliance. It equips professionals to detect threats, apply security controls, and prepare for the SY0-701+ certification. You can gain hands-on experience through virtual labs, encryption workshops, simulated incident response exercises, and real-world projects that reflect enterprise security challenges.
Our CompTIA Security+ curriculum covers network defence, encryption (TLS, AES, RSA), identity management, risk assessment, incident response, and NIST/ISO 27001 compliance. CompTIA Security+ training includes exercises in firewall configuration, vulnerability assessment, role-based access controls, encryption implementation, and zero-trust architecture principles. Participants also engage in scenario-based exercises and performance-focused labs aligned with real-world security operations.
The CompTIA Security+ course is ideal for IT professionals, graduates, and anyone seeking to start or advance a career in cybersecurity roles like Security Analyst, Security Engineer, or IT Security Consultant. Upon completion, you will receive the Edoxi CompTIA Security+ course certificate. This credential validates your skills in essential cybersecurity practices.
To know more details on our CompTIA Security+ course fees (based on learning format), syllabus, and customised corporate, online, or classroom training schedules, contact our Edoxi team.
Enrol now to build critical cybersecurity skills, enhance your career prospects, and become a trusted professional in securing enterprise IT environments.
Steps you will learn in CompTIA Security+ Course
The CompTIA Security+ (SY0-701+) exam validates your foundational cybersecurity knowledge in threat management, network security, cryptography, identity and access management, and risk mitigation. Below is a breakdown of the key exam details:
| Exam Criteria | Details |
| Exam Code | SY0-701+ |
| Exam Name |
CompTIA Security+ Certification Exam
|
| Duration | 90 minutes |
| Number of Questions |
Maximum of 90 questions, Multiple Choice and Performance-Based
|
| Passing Score | 750 on a scale of 100-900 |
| Fees |
$392 USD (price may slightly vary depending on location and currency)
|
| Certification Validity | Three years |
| Recertification |
Earn 50 Continuing Education Units (CEUs) over three years, pass the next version of the exam, or complete other approved activities
|
| Exam Administration Authority | Pearson VUE |
Gain hands-on experience in isolated networks using professional security tools for threat detection and response without impacting live systems.
Work on scenario-driven tasks that replicate real-world cybersecurity challenges in corporate environments.
Access in-depth study guides aligned with SY0-701+ objectives, including practical examples and industry best practices.
Apply symmetric and asymmetric encryption techniques using standard industry tools to secure sensitive data.
Engage in mock security breach exercises to practice detection, containment, and recovery strategies.
Learn to design and implement security systems following the “never trust, always verify” principle for network protection.
Professionals working with network infrastructure are looking to enhance their careers with specialised security skills and credentials.
Technical support professionals seeking to expand their knowledge into security operations and incident management.
Security professionals aim to validate their skills with an industry-recognised certification to advance their careers.
Individuals with basic IT knowledge looking to move into the high-demand cybersecurity field with a globally recognised credential.
Graduates with IT backgrounds seeking to strengthen their resume with specialised security skills that employers value.
Organisations looking to strengthen their security posture by upskilling their IT staff with standardised security knowledge.
Our CompTIA Security+ course in Kuwait combines expert-led training with hands-on projects based on real-world cybersecurity scenarios. Key projects include:
Set up and secure a basic network infrastructure using firewall rules and VPN tunnels to protect sensitive data transmission across insecure networks.
Identify vulnerabilities and propose mitigation strategies for a simulated business environment using industry-standard threat intelligence techniques.
Configure role-based access controls and implement multi-factor authentication protocols to secure critical systems against unauthorised access.
Implement symmetric and asymmetric encryption techniques using common tools to secure data at rest and in transit according to security best practices.
By completing our CompTIA Security+ training, you gain strong foundational cybersecurity skills. The key outcomes and career opportunities include:

Get expert assistance in getting your CompTIA Security+ Course customised!
Here’s a four-step guide to becoming a certified CompTIA Security+ professional.
Join Edoxi’s CompTIA Security+ Course
Among the many options available, Edoxi is one of the top CompTIA Security+ training centers in Kuwait. Here’s why Edoxi’s CompTIA Security+ training is the perfect fit for your needs
As a CompTIA authorised training partner, our certification-aligned curriculum is mapped to the latest CompTIA Security+ Certification Exam (SY0-701+) Objectives.
Hands-on experience in hardware labs, including implementing security controls, configuring firewalls, responding to simulated incidents, and conducting vulnerability assessments.
Edoxi has delivered corporate training for leading companies and government entities in MENA.
Flexible training options, online and corporate formats, with a 40-hour adaptable curriculum.
Certified cybersecurity professionals with expertise in threat analysis, risk management, and network security protocols.

Our mentors are leaders and experts in their fields. They can challenge and guide you on your road to success!

Sid Ahmed
Sid Ahmed is an IT network infrastructure and security trainer with over 12 years of experience at Edoxi Training Institute, Dubai. He is a certified CCNA/CCNP instructor and NSE 4 trainer and possesses advanced expertise in Cisco networking His portfolio includes prestigious Cisco certifications and hands-on knowledge of global security frameworks, making him a leader in delivering industry-relevant training.
Sid’s knowledge also extends to industry standards such as ISO 27001, NIST, SOC2, and PCI DSS, further strengthening his cybersecurity prowess.Sid Ahmed focuses on developing practical skills through hands-on training with enterprise-grade equipment. As an experienced Network and Security Architect, Sid Ahmed's expertise spans WAN/LAN, IP-MPLS, BGP, Wireless, IP Telephony, and Cybersecurity.He is skilled in HLD/LLD design, audits, pentesting, IT risk assessments, and security frameworks His specialisations include SD-WAN, VPN, VLAN, SSL, SIEM, cloud tech, and routing protocols (OSPF, BGP, STP) Sid is also proficient in Python, MySQL, JavaScript, APIs, and tools like SolarWinds, FortiSIEM, and U2000.
Here is the list of other major locations where Edoxi offers CompTIA Security+ Course
No, there are no strict prerequisites for taking the CompTIA Security+ course. It is designed for beginners and professionals alike. However, having some basic knowledge of networking, such as CompTIA Network+ level knowledge, can be beneficial.
Earning the CompTIA Security+ certification can open doors to various job roles in IT security, such as Junior Security Analyst, Security Engineer, and Security Consultant. It also enhances your credibility and may lead to higher salary prospects.
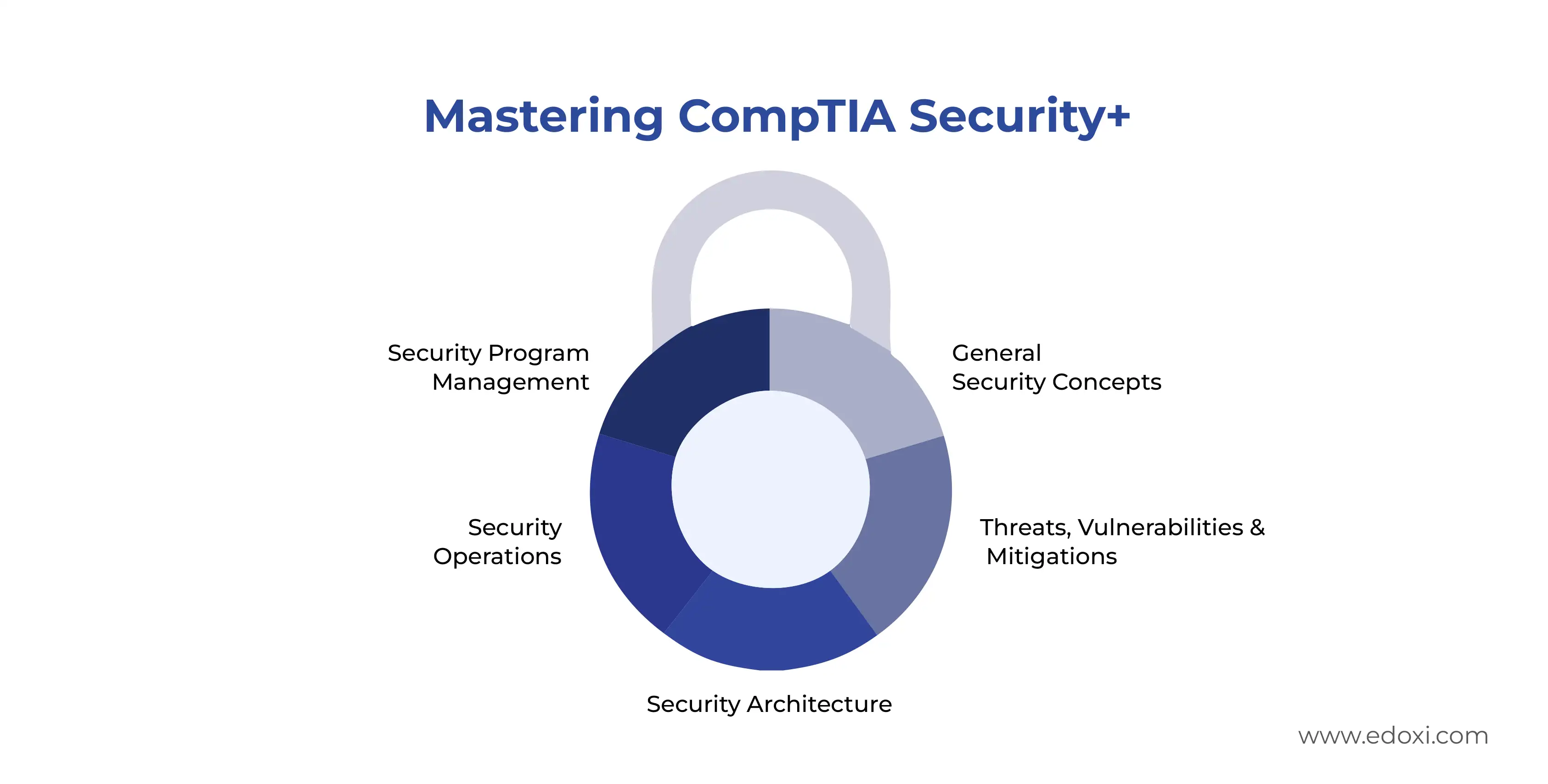
The CompTIA Security+ exam covers topics including General Security Concepts, Threats, Vulnerabilities, and Mitigations, Security Architecture, Security Operations, and Security Program Management and Oversight.
The CompTIA Security+ certification is valid for three years. You can maintain your certification by earning 50 Continuing Education Units (CEUs) over three years, passing the next version of the exam, or completing other approved activities.
The exam consists of a maximum of 90 questions, including multiple-choice and performance-based questions. The duration of the exam is 90 minutes
Edoxi offers comprehensive study materials, including up-to-date study guides, practice exams, and interactive resources. Our expert instructors provide continuous support to help you succeed in the exam.
Investing in CompTIA Security+ training ensures that your employees have a foundational understanding of cybersecurity principles, which helps in protecting your organisation's data and systems from cyber threats. Additionally, it enhances compliance with industry standards and regulations.
Yes, the CompTIA Security+ certification covers key areas of compliance, including risk management and legal, regulatory, and compliance requirements. This helps your IT team ensure that your organisation meets industry regulations such as PCI-DSS and GDPR.
Professionals with CompTIA Security+ in Kuwait can earn 1,000–3,000+ KWD per month, with related InfoSec roles reaching 12,000–17,000+ KWD annually, based on experience and employer.
CompTIA Security+ is ideal for early-career professionals seeking foundational cybersecurity skills. Here’s how it compares with other popular certifications:
| Certification | Performance-Based Questions | Vendor Neutral | Experience Level | Exam Focus |
| CompTIA Security+ | ✓ | Yes | Early career | Baseline cybersecurity skills, core cybersecurity knowledge |
| (ISC)² SSCP | Yes | Early career | Security administrator job role | |
| GIAC Security Essentials (GSEC) | ✓ | Yes | Early career | Security administrator job role |
| EC-Council CEH | Yes | Early career | Pen testing and ethical hacking | |
| ISC² Certified in Cybersecurity | Yes | Entry Level | Cybersecurity terms and concepts |
No. The course fee covers training, lab access, and study materials. The CompTIA Security+ (SY0-701+) exam voucher is purchased separately through CompTIA or authorised testing partners.
Yes. Learners receive guided access to virtual labs and practice environments during the course. Additional lab exercises and practice scenarios may also be provided for self-study, depending on the training mode selected.
Yes. The course is designed to accommodate working professionals through flexible scheduling options, including weekend batches, evening sessions, and live online training formats.
Yes. The course focuses on cybersecurity fundamentals, security operations, and defensive practices. Programming knowledge is not mandatory, although basic IT and networking familiarity is helpful.
After CompTIA Security+, learners commonly progress to certifications such as CompTIA CySA+, CEH, CCNP Security, ISO 27001 Lead Implementer, or Cloud Security certifications, depending on career goals.