Edoxi’s 35-hour CHFI Course in Kuwait is designed for cybersecurity professionals, IT specialists, and law enforcement officers. The course equips learners with practical forensic skills, investigative techniques, and industry-relevant knowledge required to handle modern security incidents and digital evidence.
Our CHFI training in Kuwait combines instructor-led sessions with hands-on lab exercises using professional forensic tools such as Autopsy, FTK Imager, and Redline. You practice real-world scenarios on Windows, Linux, and Mac systems, developing expertise in data recovery, forensic imaging, malware analysis, and evidence preservation. These exercises ensure skills are directly applicable to practical investigations and legal proceedings.
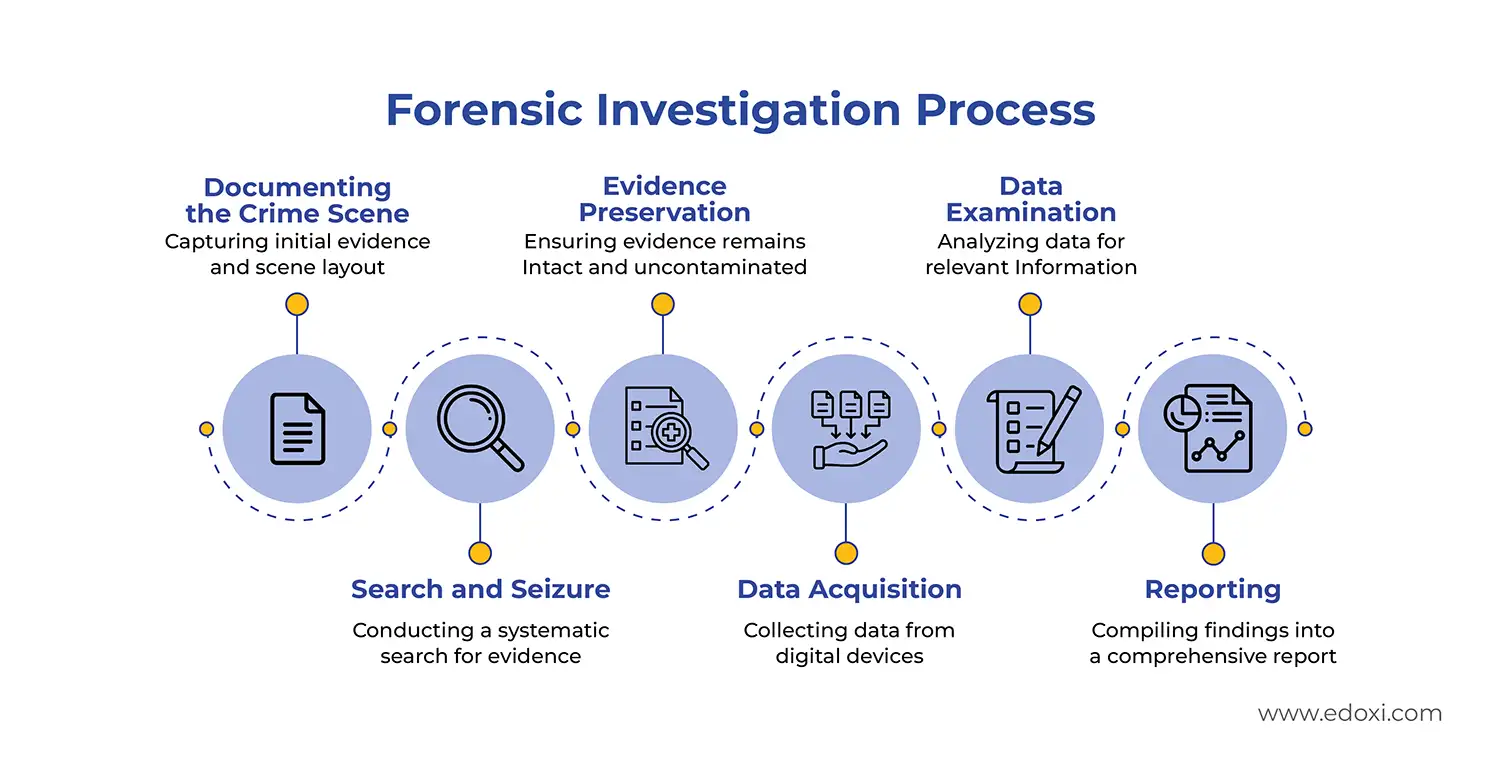
The image below outlines the CHFI certification course, featuring a curriculum focused on malware, cloud, and mobile forensics, alongside an infographic detailing the six-stage Forensic Investigation Process: from crime scene documentation and evidence preservation to data examination and final reporting.
The program also includes preparation for the EC-Council Computer Hacking Forensic Investigator (CHFI) exam, including a mock test to assess readiness and strengthen performance. Here are the key exam details of the CHFI Course:
Upon successful completion of CHFI classes, you are fully equipped to conduct forensic examinations. Exam Details
| Exam Criteria | Details |
| Exam Code | 312-49 |
| Exam Name | Computer Hacking Forensic Investigator |
| Duration | 4 hours |
| Passing Score | 60% |
| Certification Validity | 3 years |
| Recertification | Retake the exam before expiration |
| Exam Administration Authority | EC-Council |
This certification helps you analyse digital evidence, prepare court-admissible reports, and provide expert testimony.
Our course enables professionals to apply digital forensic techniques across multiple industries to investigate incidents, strengthen security, support legal processes, and manage cyber risks effectively.
Computer Hacking Forensic Investigator Course Applications Across Industries
| Domains | Practical Applications |
| Cybersecurity | Analyse cyber threats using forensic techniques, and strengthen security incident response frameworks |
| Law Enforcement | Conduct cybercrime investigations, preserve and analyse digital evidence for legal cases |
| Legal Compliance | Ensure adherence to data protection laws (GDPR, CCPA), and investigate regulatory non-compliance issues |
| Digital Forensics | Recover and analyse forensic evidence from compromised systems, detect and neutralise malware threats |
| IT Security | Investigate internal and external security breaches, and strengthen IT security policies with forensic insights |
| Corporate Risk Management | Identify cybersecurity risks affecting corporate operations, and implement forensic-based risk mitigation strategies |
Edoxi also offers CHFI corporate training for organisations, with customised delivery models designed to meet the specific requirements of enterprises and governments in cybersecurity.
For more details on the CHFI course fee, including available training options and schedules, contact our team at Edoxi.
Gain hands-on experience with industry-standard forensic tools such as Autopsy, FTK Imager, and Redline to perform professional digital investigations.
Conduct forensic examinations across Windows, Linux, and Mac operating systems to broaden your technical investigation capabilities.
Practice recovering deleted data, analysing file systems, and extracting critical digital evidence using specialised forensic techniques.
Master hex editing using the HxD tool and perform binary, decimal, and hexadecimal conversions essential for low-level data examination.
Learn proper forensic documentation practices, maintain the chain of custody, and prepare structured, court-admissible investigation reports.
Attempt a Computer Hacking Forensic Investigator (CHFI) mock test to build exam readiness and ensure a confident certification experience.
IT security specialists and analysts who want to expand their skills into digital forensics and evidence collection.
Police officers, detectives, and investigators involved in handling digital evidence and investigating cybercrimes.
Network and security professionals aiming to strengthen incident response through forensic investigation skills.
Lawyers, legal consultants, and paralegals who work on cybercrime cases and need knowledge of digital evidence procedures.
Professionals responsible for regulatory compliance and internal security breach investigations.
Enterprise security professionals looking to develop in-house capabilities for incident response and cyber investigations.
Edoxi’s CHFI Certification Course includes practical, guided activities that enable learners to apply digital forensic techniques to real-world investigation scenarios. Throughout our course, participants engage in the following hands-on learning experiences
Perform forensic investigations across Windows, Linux, and Mac systems, applying techniques to extract, preserve, and analyse digital evidence from multiple operating environments.
Work with hexadecimal data using tools such as HxD to conduct low-level analysis, edit raw data, and recover deleted or corrupted information.
Binary, Decimal, and Hex: Develop accuracy in converting binary, decimal, and hexadecimal values to strengthen raw data interpretation skills required in forensic examinations.
Create forensic disk images and recover critical data from compromised storage devices while maintaining evidence integrity and investigation reliability.
Edoxi’s MEP Design Course equips you with practical technical skills and industry-relevant knowledge to create accurate and coordinated building system designs. Here are some of the key outcomes

Get expert assistance in getting your CHFI Course customised!
Here’s a four-step guide to becoming a certified CHFI professional.
Join Edoxi’s CHFI Course
Edoxi is one of the leading training providers for CHFI Certification and cybersecurity courses. Here are the key reasons why you should choose Edoxi for CHFI Training
Recognised as an EC-Council ATC of the Year for consecutive years, demonstrating excellence in delivering globally respected cybersecurity programmes.
Our cybersecurity courses are trusted by government entities and leading organisations across the MENA region, reflecting strong industry credibility.
Benefit from discounted CHFI exam vouchers and special pricing options that make professional certification more accessible.
Train using advanced cloud labs featuring real-world scenarios, vulnerabilities, and pre-configured forensic and security tools.
Learn through EC-Council’s official curriculum, structured practical exercises, and expert-led instruction for maximum exam readiness.
Join a training institute with a strong history of successfully training thousands of professionals in cybersecurity and certification-focused programmes.

Our mentors are leaders and experts in their fields. They can challenge and guide you on your road to success!

Satendra K
Satendra Singh Khari is a renowned cybersecurity expert and the Chief Technology Officer at Edoxi, where he leads the CEH v13 AI program. With over 12 years of experience, he has trained more than 10,000 professionals and earned recognition in the Circle of Excellence for 2023 and 2024. Mr. Khari holds multiple industry certifications, including CISSP, CISM, CEH, CPENT, and CREST, which showcase his expertise in vulnerability assessment, penetration testing, and incident handling.
His practical insights, gained during his tenure as Head of Information Security in Malaysia, enhance the learning experience by providing students with essential technical skills and a clear path to career advancement. Recognized as a leader in his field, he has received the Internet 2.0 Outstanding Leadership Award for three consecutive years (2022-2024), reflecting his dedication to empowering the next generation of cybersecurity professionals.
Here is the list of other major locations where Edoxi offers CHFI Course