Edoxi’s 30-hour CISM certification course in Kuwait is designed for information security professionals aiming to advance into leadership roles in enterprise cybersecurity. This program follows ISACA’s globally recognised standards, focusing on security governance, risk management, program development, and incident management.
The course offers real-world simulations and case studies, helping participants master critical security management skills. Our hands-on training includes FAIR and OCTAVE for risk assessment and governance frameworks like COBIT and ISO 27001. These tools ensure practical competency in enterprise security management.
CISM corporate training is provided for professionals from finance, oil and gas, healthcare, and government to build strong security management skills to succeed in their careers. The curriculum prepares participants for senior roles such as Information Security Manager and CISO. Training focuses on aligning security strategies with business objectives while ensuring regulatory compliance across sectors.
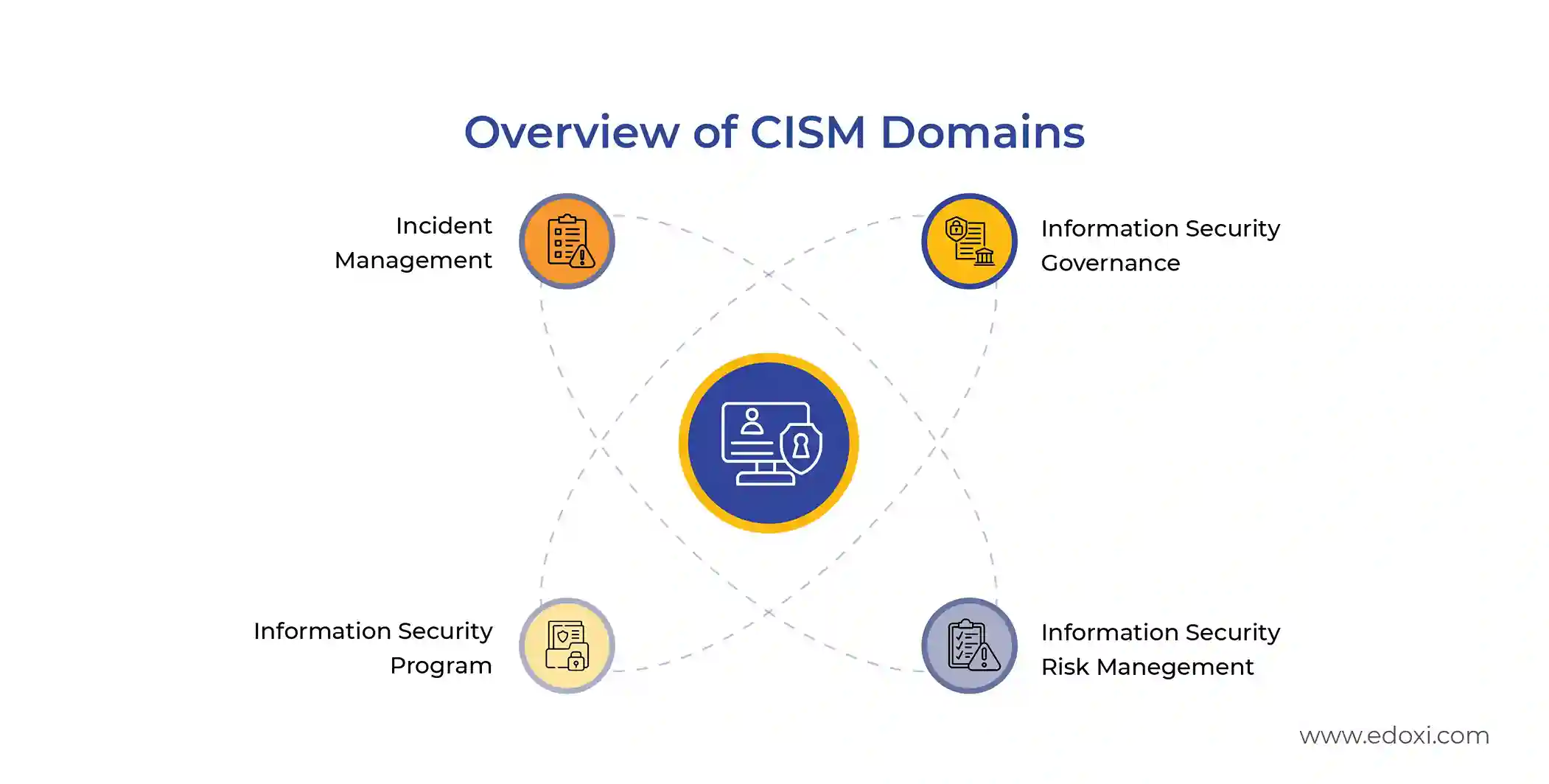
By completing this CISM course in Kuwait, professionals develop the competencies required to manage enterprise security programmes and support organisational risk management initiatives. The training prepares participants to confidently attempt the official CISM certification exam, as outlined below.
CISM Exam Details
The table below shows the CISM exam details you need to know.
| Exam Criteria | Details |
| Exam Name | Certified Information Security Manager (CISM) |
| Duration | 4 hours |
| Number of Questions | 150 multiple-choice questions |
| Passing Score | 450 out of 800 |
| Fees | 575 USD (ISACA members), 760 USD (non-members), 50 USD application fee |
| Certification Validity | 3 Years |
| Recertification | 20 CPE hours annually (120 CPE hours over 3 years) |
| Exam Administration | ISACA through PSI testing centres or remote proctoring |
For more information regarding the CISM course fee and enrollment, contact us.
Practice hands-on risk assessment and analysis through structured lab exercises focused on enterprise security scenarios.
Access ISACA's official courseware, supplemented with comprehensive mock exams and detailed case studies.
Engage in discussions and analysis of real-world security situations, with emphasis on risk management and incident handling.
Design and present a comprehensive security strategy aligned with business objectives through guided practical exercises.
Conduct detailed organisational risk analysis and develop practical mitigation strategies through hands-on projects.
Build an IT governance framework for enterprise environments through practical case studies and implementation exercises.
IT security practitioners looking to advance in security management. Ideal for those with basic knowledge of information security and IT governance.
Technical leaders managing IT infrastructure and security systems who want to strengthen their security governance and risk management capabilities.
Professionals working in risk assessment and compliance who aim to enhance their expertise in information security risk management and mitigation strategies.
Security analysts looking to progress into management roles, particularly those focused on incident response and proactive threat management.
Specialists working with regulatory requirements and governance frameworks who want to improve their security management strategies.
Professionals involved in security assessments and auditing who seek to enhance their capabilities in line with global security standards.
Our CISM training in Kuwait includes hands-on projects designed to strengthen risk management, governance planning, and incident response capabilities. Below are the key activities covered in the programme
Participants develop a comprehensive security strategy that demonstrates alignment with business objectives, providing practical experience in security program planning.
Through this hands-on project, participants conduct detailed organisational risk analysis and create practical mitigation strategies based on findings.
This project involves creating and presenting an IT governance framework for an enterprise environment, offering hands-on experience in framework development.
Students analyse actual breach scenarios and develop effective response plans, gaining practical experience in incident management.
Completing our CISM training in Kuwait equips you with the strategic and managerial skills required to lead enterprise information security programs. Key outcomes include

Get expert assistance in getting your CISM Course customised!
Here’s a four-step guide to becoming a certified CISM professional.
Join Edoxi’s CISM Course
Edoxi, leading CISM Training Institute in Kuwait, delivers industry-focused CISM training programs to build strong security management and leadership capabilities. Here are the key reasons to choose Edoxi
Learn in small batch sizes that ensure personalised attention, deeper concept clarity, and interactive discussions on real security scenarios.
Train using ISACA’s official framework, supported by real-world case studies and practical labs focused on risk management and incident response.
Strengthen your skills through risk assessment projects, security program development, and governance framework workshops that connect theory with real implementation.
Build both technical expertise and strategic decision-making abilities required for modern information security management roles through mock assessments and compliance exercises.
Access our official courseware, mock exams, and detailed case studies designed to support structured exam preparation and practical security management mastery.

Our mentors are leaders and experts in their fields. They can challenge and guide you on your road to success!

Maria Mehwish
Maria Mehwish is a forward-thinking and knowledgeable information security leader with a strong background in building, updating, and maintaining digital protections for various organisations. As a certified CEH, CCSP, CCT, and CISSP Trainer, Maria has a proven track record of delivering innovative and immersive coursework, enhancing learning experiences for cyber threats, ethical hacking, security policy, DevSecOps, and cloud security. With excellent verbal and written communication skills, she is also adept at troubleshooting problems and building successful solutions.
Maria is a self-motivated individual with a strong sense of personal responsibility, capable of managing projects from start to finish. Her expertise in Amazon Web Services, Java/Go/Python/C++, DevSecOps, computer security, Linux, penetration testing, and risk analysis, among others, makes her a valuable asset to any organisation. Maria, a British national, is a native English speaker and has intermediate proficiency in Urdu.
Here is the list of other major locations where Edoxi offers CISM Certification Course