Edoxi’s 35-hour Computer Hacking Forensic Investigator - CHFI course in London guides learners to apply computer forensic methodologies in cybercrime investigation through gathering and analysing digitally acquired evidence.
As a leading corporate training organisation, Edoxi’s CHFI course in London targets cybersecurity professionals and law enforcement officers conducting investigations for computer evidence using digital forensics and freshers who dream of becoming computer forensic investigators.
Edoxi’s CHFI course includes hands-on laboratory exercises with a variety of forensic tools such as Autopsy, FTK Imager, and Redline. Get the exclusive opportunity to investigate real-world scenarios using Windows, Linux, and Macintosh operating systems, and learn to recover data, forensically image hard drives, and analyse malware for investigation.
The CHFI course has applications across industries like:
This course also provides the necessary tools and understanding of how to successfully pass the EC-Council CHFI Certified Hacking Forensics Investigator exam and provides you with a mock test to assist with gauging your readiness for the test and enhancing your success in the examination.
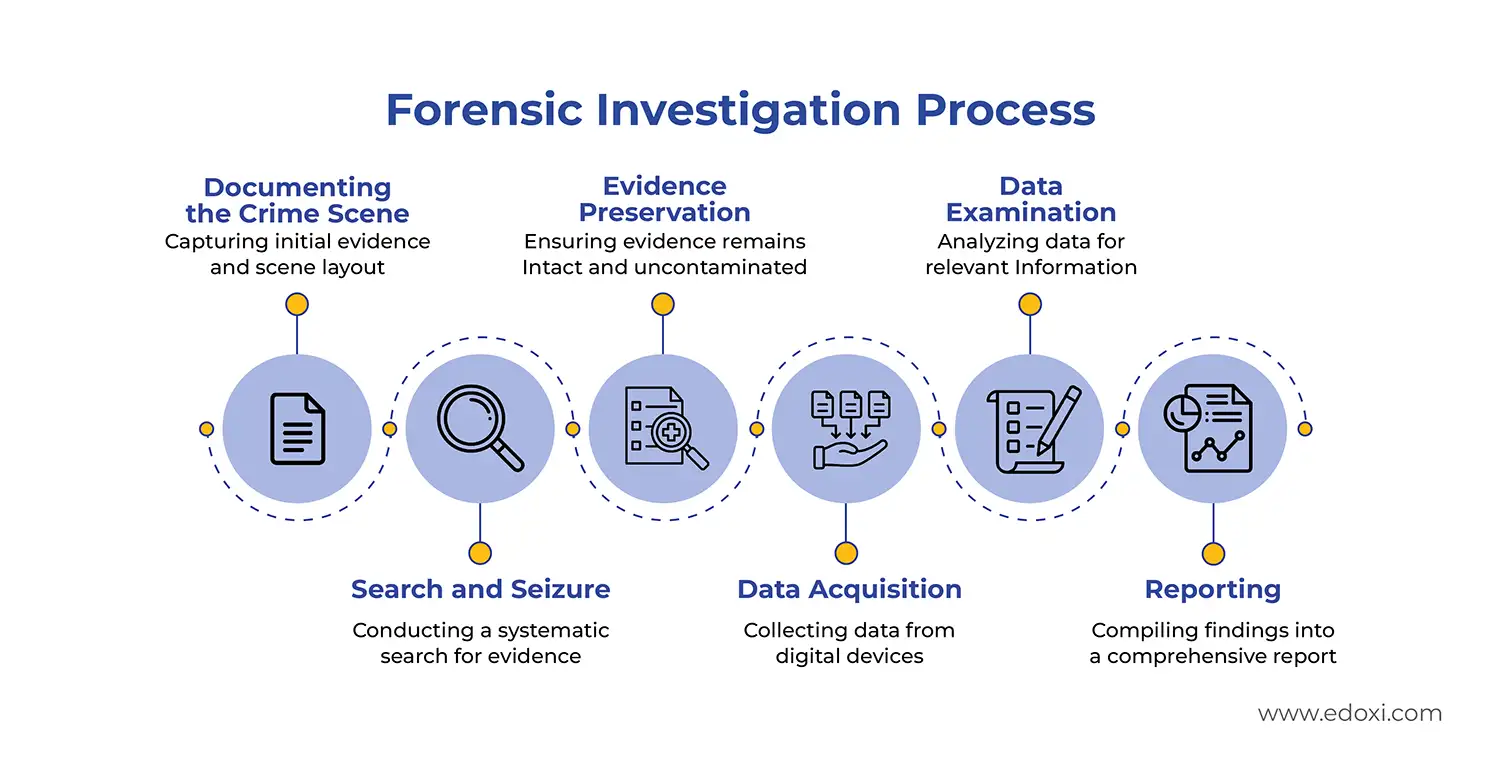
The image below outlines the CHFI certification course, featuring a curriculum focused on malware, cloud, and mobile forensics, alongside an infographic detailing the six-stage Forensic Investigation Process: from crime scene documentation and evidence preservation to data examination and final reporting.
After course completion, participants can execute proper forensic examinations, create effective court-admissible reports, and be able to testify in court. Obtaining this skillset enhances career opportunities as a valuable asset within cybersecurity teams within law enforcement agencies or corporate security divisions with regard to digital forensics expertise.
The details of the official EC_Council Exam are given:
| Exam Criteria | Details |
| Exam Code | 312-49 |
| Exam Name | Computer Hacking Forensic Investigator |
| Duration | 4 hours |
| Passing Score | 60% |
| Certification Validity | 3 years |
| Recertification | Retake the exam before expiration |
| Exam Administration Authority | EC-Council |
The course fee and schedules change according to scheduling options and customisation add-ons. Contact our team now to know more about the CHFI course in London.
Our CHFI course in London helps to gain hands-on experience with industry-standard forensic tools, including Autopsy, FTK Imager, and Redline for professional investigations.
We train your team to conduct forensic examinations across Windows, Linux, and Mac operating systems to expand your investigation capabilities.
Our data recovery and analysis labs help you to practice recovering deleted data, analysing file systems, and extracting crucial digital evidence using specialised techniques.
Master hex editing with the HxD tool and perform advanced binary, decimal, and hexadecimal conversions for data examination.
Learn to properly document findings, maintain the chain of custody, and prepare court-admissible forensic reports.
Our curated CHFI course encourages teams to take the Computer Hacking Forensic Investigator (CHFI) mock test to ensure a smooth and confident exam experience.
IT security specialists and analysts who want to expand their skills into digital forensics and evidence collection.
Police officers, detectives, and investigators involved in handling digital evidence and investigating cybercrimes.
Network and security professionals aiming to strengthen incident response through forensic investigation skills.
Lawyers, legal consultants, and paralegals who work on cybercrime cases and need knowledge of digital evidence procedures.
Professionals responsible for regulatory compliance and internal security breach investigations.
Enterprise security professionals looking to develop in-house capabilities for incident response and cyber investigations.
Edoxi has created an overall CHFI course that teaches teams to apply digital forensic techniques through hands-on guided activities that simulate real-life investigations. The following hands-on activities are completed in our CHFI course in London:
Your team get to perform forensic analyses of multiple operating systems (Windows, Linux, and Mac) utilising digital forensic techniques that can be used to extract, preserve, and analyse digital evidence from all three types of computer systems.
Master the skills to use hexadecimal values to perform low-level analysis, edit raw data, and recover deleted or corrupted data by using HxD (or any other hex editor).
Develop accurate skills in converting binary, decimal, and hexadecimal numbers to easily interpret raw data when performing digital forensic examinations.
We guide you to create forensic images of disks or disk images and recover important data from a compromised storage device or disk image while still preserving the integrity of the evidence and reliability of the investigation.
Edoxi’s CHFI course in London equips you with practical technical skills and industry-relevant knowledge in cyber forensics. Here are some of the key outcomes:

Get expert assistance in getting your CHFI Course customised!
Here’s a four-step guide to becoming a certified CHFI professional.
Join Edoxi’s CHFI Course
The major reasons to choose Edoxi for your CHFI training in London:
Edoxi has offered cybersecurity training for government entities and leading companies in London.
Enjoy discounted CHFI exam vouchers and special rates for your practical certification exam.
Practice in advanced cloud labs with real-world scenarios, vulnerabilities, and pre-configured security tools.
Follow EC-Council's official curriculum, practical exercises, and expert instruction.
Trained over 10,000 professionals with a consistent record of success in certifications and career advancement.
Your team can gain practical experience through simulated cybercrime investigations, forensic analysis exercises, and real-world case studies designed to build digital forensics skills.

Our mentors are leaders and experts in their fields. They can challenge and guide you on your road to success!

Maria Mehwish
Maria Mehwish is a forward-thinking and knowledgeable information security leader with a strong background in building, updating, and maintaining digital protections for various organisations. As a certified CEH, CCSP, CCT, and CISSP Trainer, Maria has a proven track record of delivering innovative and immersive coursework, enhancing learning experiences for cyber threats, ethical hacking, security policy, DevSecOps, and cloud security. With excellent verbal and written communication skills, she is also adept at troubleshooting problems and building successful solutions.
Maria is a self-motivated individual with a strong sense of personal responsibility, capable of managing projects from start to finish. Her expertise in Amazon Web Services, Java/Go/Python/C++, DevSecOps, computer security, Linux, penetration testing, and risk analysis, among others, makes her a valuable asset to any organisation. Maria, a British national, is a native English speaker and has intermediate proficiency in Urdu.
Here is the list of other major locations where Edoxi offers CHFI Course
The following related courses can be done after completing our CHFI course in London: